Cyber threats are also changing with each passing day, and no organization can afford to solely use the basic defenses. They should instead proactively test their environments to identify weak areas before exposing attackers to them. This is precisely where Red team tools are important. These tools enable security experts to test real-world attacks by simulating and revealing the hidden vulnerabilities as well as enhancing the defensive mechanisms, before any damage.
Tools, however, do not ensure security. Teams should utilize them strategically, and above all, they should work in teams. Consequently, purple teaming has become one of the methods through which many organizations merge offensive and defensive knowledge.
With this guide, you will get to know what tools red teams are based on, why they are important, and how purple teams use them efficiently. Furthermore, you are going to learn how this partnership will take security to the next level, rather than being reactive.
Red Team Tools That Power Effective Penetration Testing
Security professionals choose tools based on attack goals, infrastructure type, and testing scope. Nevertheless, the most effective red teams select tools that replicate real attacker behavior while generating actionable insights.
1. Reconnaissance Tools for Intelligence Gathering
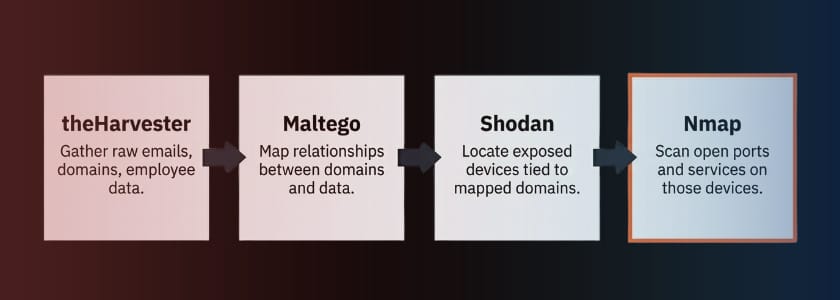
Red teams gather as much information as they can before launching any attack simulation. As a result, reconnaissance tools assist them in mapping the networks, detecting as sets and locating entry points.
Common reconnaissance tools include:
- Nmap for scanning open ports and services
- Maltego and the Harvester for OSINT (emails, domains, employee data)
- Shodan for finding exposed devices on the internet
As an illustration, the network scanners easily uncover open ports and running services. Moreover, OSINT models collect publicly accessible data like emails or stolen credentials. The intelligence allows the testers to develop specific attacks instead of guessing.
Organizations using Red tools to investigate the external landscape have a clear view of their external exposure. Thus, they have the ability to rectify the weaknesses promptly rather than responding when there is a breach.
2. Exploitation Frameworks That Simulate Real Attacks
Red teams then make controlled attempts at exploitation after intelligence collection. At this point, they apply frameworks that imitate methods that attackers are actively using. They assist testers in verifying the real presence of compromise as a result of a vulnerability. In the absence of this, security teams may overrate their protection.
Popular exploitation tools include:
- Metasploit Framework for exploiting vulnerabilities
- Cobalt Strike for command-and-control simulations
- Core Impact for professional penetration testing
Organizations that exploit red team tools no longer have to exist on theoretical risk. Rather, they visualize the way an attacker can advance in their environment. This means that leadership will be able to focus on remediation through actual impact as opposed to presumption.
3. Credential Access and Password Testing Tools
Weak credentials are still amongst the simplest ways of accessing corporate networks. Thus, red teams proactively challenge password hygiene and authentication.
Common tools include:
- Mimikatz for credential dumping
- Hydra and John the Ripper for password cracking
- Hashcat for testing password strength
The password auditing tools detect reused credentials, weak combinations, passwords, and improperly configured policies. In the meantime, credential dumping tools show how acollect collects the data of the logins after gaining access.
In cases where security teams incorporate the red team tools to test the credentials, they will frequently identify security risks that are under the radar. Consequently, organizations have a stricter password policy, multi-factor authentication, and fewer attacks based on user accounts.
4. Post-Exploitation and Lateral Movement Tools
After gaining access to a network, attackers work quietly to access valuable assets. Thus, red teams are used to approach laterally to test segmentation and access.
Common tools include:
- BloodHound to map Active Directory relationships
- PowerShell Empire for internal movement
- PsExec for remote execution
Post-exploitation tools point out too many permissions, unpatche,d systems and trusts. Furthermore, they demonstrate that such a small concession may turn into a serious event.
Companies experience increased transparency of weaknesses within the organization when they incorporate team tools in the post-exploitation testing. Consequently, they reorganize privileges and enhance network borders.
How Purple Teams Integrate Red Team Tools for Maximum Impact
As much as the weaknesses are exposed during red team exercises, they become more valuable when defenders are involved. It is precisely the reason why purple teaming has been spreading. Teams work together on an ongoing basis.
Real Life Example:
A large U.S. food production company ran a purple team simulation where phishing emails bypassed filters and led dozens of employees to click malicious links, revealing both human and technical security gaps.
1. Converting Attack Data to Defensive Intelligence
The Purple team will read the output of the red team tools and convert it into defensive improvements. As an example, when a payload is not detected, it is looked into by the defenders, and rules are changed accordingly.
This fast feedback mechanism enhances security maturity. Furthermore, teams prevent the occurrence of repetitive mistakes owing to the fact that they learn in real time.
2. Enhancing Detection Engineering
Gaps in detection remain unseen until soputsill put them into test. Nevertheless, purple teams actively activate red team tools to cause alerts in order to test the capabilities of monitoring.
In case alerts do not work, analysts redefine signatures and behavioral analytics. As a result, organizations are able to identify threats promptly and minimise response times.
3. Enhancing Response to Incidents
Defenders are given realistic practice by simulated attacks. Thus, purple teams also carry out response exercises, which depend on scenarios generated using the tools of the red team.
In such exercises, the responders define bottlenecks, demystify roles, and simplify communications. Consequently, they deal with actual cases more confidently and quickly.
4. Promoting the Sharing of Knowledge
Teamwork is also healthy when the teams exchange insights freely. Purple teams go through strategies jointly, discuss the reasoning of the attacker, and talk about defense strategies.
Since the tool of red teams reveals real attack paths, the defenders have practical knowledge and not theoretical knowledge. The overall security capability is therefore strengthened.
Best Practices for Integrating Tools Successfully
Organizations need to be strategic when it comes to collaboration in order to capitalize on the outcome. The first thing is to state specific goals. The best red team tools generate piecemeal insights even without direction.
Secondly, keep the attackers and defenders transparent. Despite the merits of controlled secrecy, structured debriefings will make sure that everybody is befromng out of the exercise. Automatize when it is possible, but watch the outcomes. Techniques produce information; the human mind produces knowledge.
Lastly, consider purple teaming as a continuous process and not an event. Constant testing keeps defenses up to date with threats.
Real Life Example:
A UK gas industry organization hired a red team that successfully entered secure facilities by tailgating staff and posing as maintenance personnel, exposing major policy enforcement gaps.
The Future of Collaborative Security Testing
Cybersecurity has been shifting to cooperation. Whereas red teams sharpen offensive, purple teams make sure that all lessons enhance defense.
Comthaties who invest in red team tools and workflows create partnerships and put themselves in the lead over their competitors. Moreover, they also make testing a strategic value rather than a compliance check. The threats are becoming more advanced, and individual efforts will not be enough. Nonetheless, cross-functional teams develop flexible security initiatives that can withstand contemporary attacks.
Conclusion
Contemporary security requires more than firewalls and antivirus software. It involves real-world testing, quick learning and teamwork. Red team tools enable an organization to identify areas of weakness before the attackers can, and purple teaming transforms these findings into quantifiably better ones.
By collaborating, teams no longer pursue threats but prepare for them. Thus, the businesses not only safeguard their resources but also gain confidence among customers and stakeholders.
Frequently Asked Questions
1. What are red team tools used for?
Red team tools assist the security personnel in simulating cyberattacks, determining vulnerabilities, and determining the level at which the defenses perform under real-life conditions. Because of this, organizations are able to address any weaknesses or their exploitation by their rivals.
2. How do purple teams benefit from these tools?
Purple teams utilize knowledge that is generated by Red team tools to develop a better detection rule, response workflow, and security posture. Furthermore, cooperation will make sure that all the simulated attacks result in quantifiable improvements.
3. Should small organizations invest in red and purple teaming?
Yes, since smaller businesses that have fewer defenses are the target of attackers. The adoption of tools and collaborative testing at an early stage of the Red team helps organizations to minimize risks, enhance preparedness, and establish a scalable security foundation to continue their growth.