The field of cybersecurity is constantly developing at a fast pace, and thus, companies need to be smarter and more collaborative. Most of the professionals will come across the phrase Red vs Blue Team, but do not clearly comprehend how it relates to the Purple Team. Such confusion may undermine security strategies since every team is of the essence.
Simply put, Red vs Blue Team is an attack and defense strategy. Nonetheless, the purple team introduces teamwork into this model. Besides, it makes sure that organizations not only test systems but also continue to enhance them as well. Thus, to enhance your cybersecurity position, you will have to have a clear understanding of how these teams collaborate.
Understanding Red vs Blue Team in Cybersecurity
The Red vs Blue Team model is a manifestation of two contrary sides in cybersecurity. The red team is the attackers, with the blue team being defensive. Accordingly, through such an arrangement, organizations can recreate real-world cyberthreats in a controlled environment.
Phishing, exploitation, and social engineering are methods of exploiting loopholes that the red team employs in order to challenge the weakness of the system. In the meantime, the blue team tracks systems, identifies suspicious actions, and reacts to threats. Besides, such interaction assists organizations in assessing their current security posture.
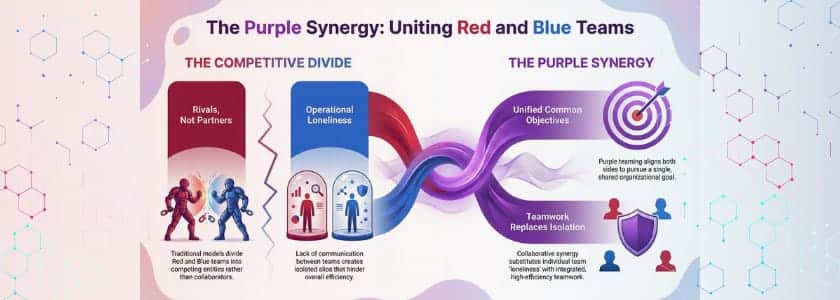
The Red vs Blue Team model, however, sometimes creates a gap. Due to the fact that both teams operate independently, they might not be able to exchange ideas. Through this, organizations do not have a chance to enhance their defenses in a hurry.
What Does the Red Team Do?
The red team is concentrated on offensive security testing. It proactively emulates cyberattacks in order to determine the vulnerabilities before the actual attackers can use them. Thus, organizations are able to know how their systems perform under pressure.
In addition, the red team takes real-life tactics to implement simulations. As an illustration, they can either make phishing attacks or misuse misconfigurations. Consequently, they discover latent weaknesses that cannot be detected by automated tools.
Besides, the red team assists organizations in thinking like attackers. This view is desirable because it enhances planning of security and also assures that security defenses are in place against real threats rather than hypothetical threats.
Real Life Example:
The Equifax data breach exposed sensitive data of over 147 million users, highlighting why red teams simulate attacks to identify vulnerabilities before real attackers exploit them.
What Does the Blue Team Do?
The blue team is concerned with the defensive operations. It secures systems, identifies threats, and reacts to incidents in real-time. As such, it is vital to ensure that the system is kept intact.
In addition, SIEM systems, firewalls, and monitoring solutions are the tools that are being used by the blue team to detect suspicious activities. Consequently, it is able to react fast and reduce losses.
The blue team also constantly enhances the detection rules and response strategies. Thu,s it will keep the organization ready to change cyber threats.
Real Life Example:
During the Maersk NotPetya cyberattack, the blue team mitigated ransomware spread across 600+ locations, showing how defensive teams respond to real-time threats.
What Is the Purple Team Concept?
The purple team is the one that fills the gap between the red and blue teams. Both teams work together and exchange knowledge as opposed to working individually. As such, organizations enhance the simulation of attacks as well as defense.
In addition, the purple team makes sure that all red team operations bring about quantifiable changes in blue team defenses. Consequently, organizations attain expeditious learning and enhanced security results.
Also, the purple team establishes the feedback loop. This cycle enables the teams to improve their strategies every time and to effectively adjust to emerging threats.
How Red vs Blue Team Evolves with Purple Teaming
Red vs Blue Team model is furthermore efficient with purple teaming introduced in organizations. They do not divide red and blue teams as rivals but pursue a common objective. Thus, teamwork substitutes loneliness.
As an example, the red team can show the way it circumvented a security control. In the meantime, the blue team examines the opening and advances the detection right now. Consequently, the organizations state that repairing the vulnerabilities sooner.
Besides, this style promotes continuous improvement. Due to real-time knowledge sharing in teams, teams minimize the possibility of instances of mistakes. Hence, security is more flexible and robust.
Key Benefits of Red, Blue, and Purple Teaming
The red, blue, and purple teams are a good combination that has a number of advantages. The first is that it enhances the visibility of security. Since organizations are testing and monitoring systems and are doing this on a continuous basis, they are able to get more insight into the vulnerabilities.
Second, it improves response capacities. The blue team also gets lessons with the red team and thus can react to an actual threat better.
Besides, it develops a proactive security culture. Organizations are ready to respond to incidents instead of responding to them at the time. Consequently, this makes them less vulnerable to cyberattacks and makes them more resilient.
According to Verizon, ransomware accounted for 24% of all breaches in 2023, highlighting the importance of proactive red, blue, and purple team strategies.
Best Practices for Effective Team Collaboration
The Red vs Blue Team model is to be maximized by the best practices in organizations. To begin with, they have to establish clear objectives for every exercise. Hence, teams are able to work on quantifiable results.
Then, they ought to promote free communication. Since teamwork fosters progress, teams need to disseminate results without reservation.
Further, real-life situations should be utilized by the organizations. This method will make sure that simulations represent real threats. This leads to hands-on experience and increases the level of preparedness of teams.
Conclusion
Cybersecurity should not be done in a vacuum. Red vs Blue Team model offers a solid base through the unitary union of attack and defense. Nevertheless, this approach is advanced with the introduction of the purple team.
Organizations make better detectives, responders, and generally more resilient through collaboration. Besides, they establish a cycle of continuous improvement that is responsive to the changing threats.
So, in case you would like to enhance your security strategy, you will have to implement this integrated strategy. Not only does it increase your defenses, but it also makes your organization ready for other challenges ahead.
Frequently Asked Questions
What is the Red vs Blue Team in cybersecurity?
Red vs Blue Team model entails the use of attackers and defenders in countering each other to test and enhance security systems. It aids organizations in determining weak areas and reinforcement.
What is the role of a purple team?
The purple also links the red and blue teams. It maintains cooperation, enhances communication, and makes organizations learn from each security test.
Why is Red vs Blue Team important?
Red vs Blue Team technique is used to assist organizations in mimicking real-world attacks and enhancing defense. Thus, it enhances cybersecurity, in general, and minimizes threats. Learn attacks and improve defenses. Therefore, it strengthens overall cybersecurity and reduces risks.





