To be successful in offensive security, you cannot afford to work on theory. Rather, you need to be adept at using the appropriate tools for red team operations that would simulate real-world attacks.
Nevertheless, lots of beginners are confused as they are not aware of which tools are really important. They therefore end up wasting time searching and selecting random software rather than developing a focused toolkit.
Core Categories of Tools for Red Team Operations
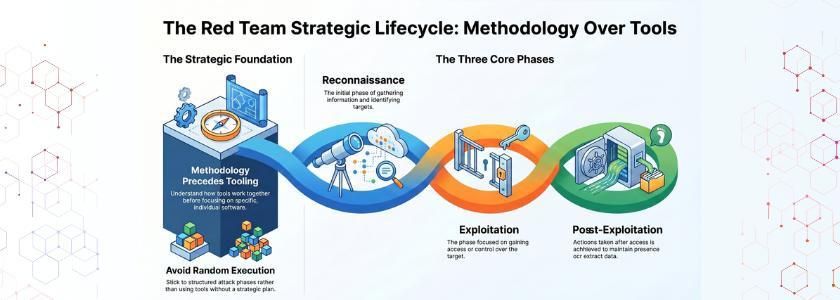
You have to learn how the tools for the red team work together before getting down to specific tools. You should stick to attack phases like reconnaissance, exploitation, and post-exploitation as opposed to using them randomly.
So, all the tools you employ should have a definite aim. An example would be some of the tools that collect information, as well as those that assist you in gaining access or persisting. Once you know this structure, you will also find that learning will be much faster and more effective.
According to Verizon DBIR, over 80% of breaches involve stolen or weak credentials, reinforcing the need for strong red team tooling.
Most Essential Tools for Red Team
This guide will help you learn the most important tools of red team operators, why they are important, and how you can effectively use them. As well, you will learn how to merge them into a realistic workflow that reflects the actual interactions.
1. Reconnaissance Tools
To begin with, reconnaissance is the initial operation of each red team operation. You cannot make successful attacks unless you have proper intelligence.
Maltego and Recon-ng are tools that assist you in gathering information on target areas, such as domains, workers, and infrastructure. Additionally, the tools automate the collection of information and will therefore save time and increase accuracy.
2. Exploitation Tools
After you find the weakness, you must have the exploitation tools. At this point, tools for the red team are more severe, action-oriented.
Metasploit is one of the most popular frameworks. It gives you the ability to take advantage of the known vulnerabilities and achieve preliminary access to the systems. Moreover, it eases complicated attacks by using prebuilt.
3. Credential Access Tools
Once you have access, you are likely to require credentials to gain access further into the network. This is where tools such as Mimikatz are involved. Mimikatz uses memory to retrieve passwords, hashes, and Kerberos tickets. Consequently, you are able to upscale privileges and impersonate users.
Likewise, brute-force attack tools such as Hydra assist in cracking into login systems by means of a brute-force attack. Brute force is simple; still, it is effective in an environment with low security levels. Credential access tools are thus still an important aspect of contemporary red team activities.
Real Life Example
In 2021, Colonial Pipeline suffered a ransomware attack due to compromised credentials, highlighting the importance of credential access tools.
4. Post-Exploitation Tools
After getting into the system, you have a different objective. You do not want to access; now you want to persist and move laterally.
Such tools as Cobalt Strike offer high-end features of command-and-control activities. They enable you to keep access, remotely execute commands, and move between systems.
5. Lateral Movement Tools
Once you have a foothold, you need to increase your reach. This is where tools of lateral movement prove necessary.
PsExec is a utility that enables you to run commands on computers. In the meantime, BloodHound can be used to map relationships in Active Directory setups.
6. Web Application Tools
Organizations use web applications. Thus, the red team has a specific need for web-based tools. Burp Suite is an impressive software that is used to test web vulnerabilities. It enables you to intercept requests, manipulate data, and discover vulnerabilities.
Likewise, OWASP ZAP is an automated tool that scans for common vulnerabilities. In spite of the assistance of automation, manual testing is also essential.
7. Evasion and Obfuscation Tools
Evasion is one of the skills as defenses are enhanced. Thus, the tools for the red team are based on avoiding detection systems.
Some software, such as Vei, is used to create payloads that avoid detection by antivirus programs. In the meantime, Shellter is altering executables to prevent detection.
8. Wireless and Network Attack Tools
Not every attack occurs within the wired networks. In most instances, wireless networks are a point of entry. Aircrack-ng cracks Wi-Fi passwords and analyzes wireless traffic. On the same note, Kismet identifies networks and tracks activity.
Organizations often overlook wireless security, as such tools present a new opportunity for attackers. Hence, incorporate them into your toolkit to make your approach more complete.
9. Social Engineering Tools
Technology is not enough to protect systems. Man is a creature who can be the most vulnerable.
Applications such as the Social-Engineer Toolkit (SET) are used to simulate phishing attacks and credential harvesting. Consequently, you will be able to check how the employees will react to the real-life situations.
10. Reporting Tools
Lastly, once exploited, your job is not over. You should understandably record your findings.
Such tools as Dradis and Faraday are used to facilitate the results and create reports. Since clients are dependent on such reports, it is necessary to be clear.
How to Build Your Red Team Toolkit
With the tools that you have learned to be the most important in the red team, you may be wondering how to begin. To begin with, work on learning one tool in each category. Next, slowly build up your toolkit. Rather than going out to chase each new tool, go for depth, and not breadth.
The second one is regular practice in laboratories and simulations in the real world. Since you do not become skilled by having tools, but rather through hands-on experience. Finally, stay updated. There is a high rate of cybersecurity changes, and thus, there is a need to undergo continuous learning.
Conclusion
Learning how to use the correct tools to use in red team operations can change your experience in cybersecurity. Nonetheless, you can never be successful merely because of the tools. Rather, it is your skill to think critically and to adapt to various situations that defines your level of skill.
The point is: it is much better to begin with anything little, be consistent in it, and practice regularly. In the long run, you will not only gain knowledge of the tools but also the way real attackers work. It is then that you will actually become a red team operator.
Frequently Asked Questions
1. What are the most important tools for red team beginners?
Nmap, Metasploit, and Burp Suite should be the beginning for those who are inexperienced. These tools include scanning, exploitation,n and web testing, ng which are the pillars of red team activities.
2. Do I need to learn all the tools for red team operations?
No, you don’t need to learn everything at once. Rather, make sure to work on the major categories, and as you become more experienced and confident, you can continue to deepen your knowledge base.
3. Are the tools for the red team enough to become a professional?
No, it is not possible to use tools alone. You are also required to know the attack strategies, network, and system security. Major contributing factors are practical experience and critical thinking.




