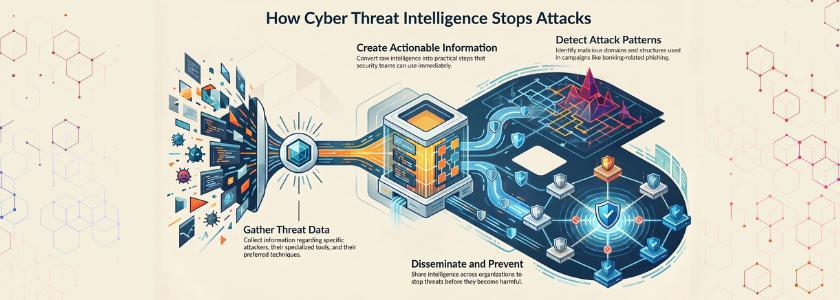
Cyber Thread Intelligence, in simple terms, gathers information about attackers, their tools and techniques, and converts it into actionable information. To illustrate, when a security team becomes aware of a new phishing campaign targeting banking users, it examines the attack pattern, detects malicious domains, and disseminates this information to other organizations. This means that others will be able to prevent these threats before they become harmful.
Besides, CTI is not only detection-oriented. Rather, it makes you comprehend the reasons why an attack occurred and the spread of it. Thus, you can better understand the actions and motives of attackers.
How Cyber Thread Intelligence Works in Practice
You need to observe Cyber Thread Intelligence in action to get a sense of its operation in real-life situations. First, systems gather data that is based on various sources, which may include logs, endpoints, and network traffic. Analysts then subject this data to come up with suspicious patterns.
They then compare these patterns with intelligence feeds of known threats. The true value, however, er lies when they make sense of the information and come up with actionable insights.
An example is that, in case several organizations report the same malware signature, CTI systems recognize it as a new threat. Hence, security teams are able to prevent it beforehand.
Real Example of CTI in Action
Cyber Thread Intelligence can be applied practically in detecting ransomware. Imagine a worldwide ransomware attack on the healthcare systems. Several hospitals are found to have abnormal encryption activities, which are identified by security analysts.
Afterward, they deconstruct the malware code and find a general attack pattern. Additionally, they exchange indicators of compromise (IOC), including file hash and IP addresses. Consequently, other healthcare organizations will be able to thwart the attack prior to infection. Thus, CTI minimizes the damage.
In addition, this process underscores the ways in which CTI converts individual attacks into worldwide defense measures. Organizations fight together and protect each other as opposed to operating independently.
Real Life Example:
Security researchers used Cyber Threat Intelligence to discover a kill-switch domain in WannaCry malware, which helped slow down the global ransomware outbreak.
Why Cyber Thread Intelligence Matters
The significance of Cyber Thread Intelligence in the current cybersecurity landscape cannot be overlooked. One, it enhances the rate of detecting threats. You do not wait till an attack is successful,u l but you spot it at the onset.
Second, it enhances decision-making. CTI allows security teams to give a priority to risks based on real-world information. In addition, this assists organizations in making resource allocations efficiently.
Nevertheless, the greatest benefit of it is prevention. CTI does not mean responding to threats, but rather being able to anticipate them. Thus, companies adopting CTI have a considerable security edge compared to those that adopt reactive-only strategies.
Global cybercrime damages are projected to reach $10.5 trillion annually by 2025, highlighting the growing importance of threat intelligence in defense strategies.
Components of CTI
In order to gain a complete knowledge of CTI, it is important to be acquainted with its major components. To begin with, there are significant roles in data collection. Systems collect endpoint, network, and external feed information.
Second, analysis converts raw data to meaningful information. Data will not be useful without analysis. Third, dissemination is needed to make sure that intelligence is available to the appropriate teams. In addition, information sharing enhances shared defense.
Lastly, the system is refined by feedback. CTI is constantly changing, as there are new threats. Thus, Cyber Thread Intelligence will be a dynamic process, but not a tool.
Challenges in Implementing CTI
CTI, as powerful as it is, has challenges that organizations encounter in the implementation process. To begin with, there is data overload, which causes a challenge. Analysts often feel overwhelmed by too much information.
Second, the inadequacy of competent professionals hinders performance. Without relevant expertise, analysts may misinterpret intelligence. In addition, problems in integration also tend to occur. Lots of systems lack efficiency in communication, hence decreasing visibility.
Nonetheless, automation, training work teams, and enhancing system integration will help organizations to counteract these difficulties. Through this, Cyber Thread Intelligence will be efficient and effective.
Best Practices for Effective CTI
Best practices need to maximize the value of CTI. To begin with, consider pertinent sources of data. Not every data is useful, and therefore, look at quality and not quantity.
Then automate repetitive processes. Automation helps to decrease workload and enhance accuracy. Also, promote inter-team cooperation. Teams exchange knowledge, it cause the enhancement of CTI.
In addition, you should keep threat intelligence feeds up to date. Threats in cyberspace change rapidly; thus, obsolete information makes little sense. Lastly, make CTI a part of your security plan. This will make sure that intelligence is directly in support of defense actions.
Future of Cyber Threat Intelligence
The future of cybersecurity heavily depends on Cyber Thread Intelligence. With the sophisticated attacks that are increasing, organizations have to depend on smart systems in order to be safe.
Further, the usage of artificial intelligence and machine learning can improve CTI. The technologies will aid in the faster and more accurate detection of threats.
Also, automation will have a significant impact. Threats respond automatically without human intervention. However, human skills will still play an important role, and analysts will understand complex threats and guide the decision-making process.
Thus, CTI will keep developing as one of the essential aspects of cybersecurity defense.
Conclusion
Cyber threats are rising, and organisations need to keep up with the rapid change in order to remain secure. Thus, Cyber Thread Intelligence is a highly important concept that should be comprehended in current cybersecurity practices.
When you find out what an example of CTI is, you see how potent this strategy can be in a real-world situation. It assists you in identifying threats at an early stage, reacting more quickly, and avoiding major destruction.
Finally, CTI will simplify your life by enabling you to be at the forefront of the attackers and create a more robust security posture in an ever-more-hostile digital world.
Frequently Asked Questions
1. What is an example of Cyber Thread Intelligence?
One of them is the identification of a ransomware campaign, monitoring its activity, and disseminating hints of compromise to stop additional infections within the organizations.
2. How does Cyber Thread Intelligence help organizations?
It assists organizations to identify the threat in their early stages, comprehend the behavior of attackers, and reacting more quickly to limit the losses and enhance the overall security.
3. Is Cyber Thread Intelligence only for large companies?
No, CTI can be utilized in organizations of any size. The use of threat intelligence feeds and automated security tools is beneficial even to small businesses.