Technology operational settings require accuracy, care, and profound understanding. The OT systems are unlike the IT systems that manage physical processes and thus, errors have the potential to cause physical damage. Organizations should thus ensure that they come up with secure and controlled exercises that would deal with OT-specific threats without interfering with the activities. You will get to know how to plan, implement, and take advantage of such exercises in a way that ensures safety, compliance, and continuity of operations in this blog.
Moreover, these exercises help teams identify vulnerabilities before they are exploited. Additionally, they strengthen incident response capabilities across both OT and IT domains.
Why Safe Exercises Must Address OT-Specific Threats
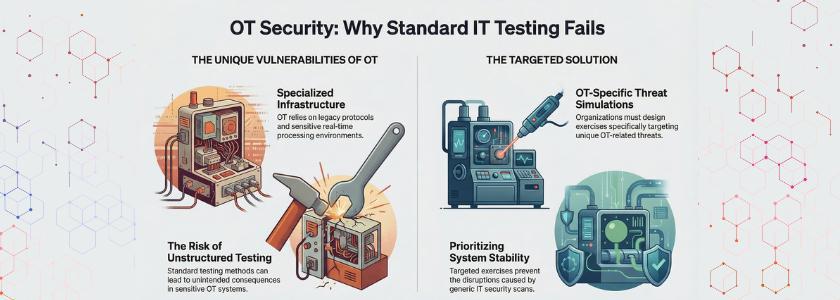
Firstly, the OT environments are vastly different when compared to the conventional IT systems. They are based on the use of legacy protocol, real-time processing, and infrastructure that is highly sensitive. Therefore, when these systems are tested in an unstructured manner, they may end up getting these unintended consequences. This is the reason why organizations need to target OT-related threats in simulations and exercises.
As an example, attackers usually attack the PLCs, SCADA systems, and industrial protocols. These vectors are not like the normal IT attack surfaces. Consequently, your exercises should be based on realistic situations on the use of OT-specific threats and not generic cyber incidents.
Real Life Example:
The Stuxnet malware specifically targeted industrial control equipment (PLCs) in a nuclear facility, manipulating operational processes and representing one of the first major OT‑specific threats ever documented
Designing Controlled OT Security Exercises
The first is the definition of clear objectives. You should decide what you want to test, e.g., incident response, detection capabilities, or communication workflows. After completing this, you need to correlate these objectives with the familiar OT-specific threats to make them relevant.
Secondly, develop a controlled environment. Many organizations use digital twins or test laboratories to model industrial processes. This would enable the teams to test without endangering real systems. Besides, it makes exercises safe and repeatable.
Then, you are to engage cross-functional teams. OT security involves the cooperation of the engineers, IT personnel, and cybersecurity experts. As such, the involvement of all the concerned parties is very important. Such a partnership enhances organization and delivers achievable results.
Ransomware attacks against industrial organizations increased by 87% in 2022, with 605 incidents tracked targeting OT/ICS environments.
Real Life Example:
In the Colonial Pipeline ransomware attack, attackers hit the company’s systems in 2021, forcing the shutdown of pipeline operations out of caution to prevent spread to OT systems — highlighting how IT breaches can drive OT disruption.
Key Types of OT Security Exercises
There are various forms of exercises that an organization can adopt based on its level of maturity. All the formats have a different approach to OT-specific threats and are also safe.
Tabletop Exercises
One, tabletop exercises offer a form of discussion. Teams are taken through theoretical situations without having to deal with live systems. In this way, the participants will be able to analyze the OT-specific threats in a risk-free setting. Besides, it enhances decision-making and communication.
Simulation-Based Exercises
Simulation-based exercises are then used to mimic real-world attacks. These activities enable the teams to train how to identify and react to OT-specific threats with realistic information. Consequently, the participants will acquire experience on the ground without impacting operations.
Red Team / Blue Team Workouts.
In addition, the simulation of adversarial behaviour is done through red and blue team exercises. The red team is the imitator of attackers and the blue team is the defender of the system. These exercises, when developed with care,e point out their weaknesses in reference to OT-specific threats and enhance resilience.
Best Practices for Effective OT Exercises
In order to get significant outcomes, you need to observe best practices. The practices will also make sure that your exercises are safe, relevant and impactful.
- To begin with, one should always begin small. Simple scenarios should be used initially, and then more complex scenarios should be introduced. This strategy is useful because it assists the teams in gaining confidence and acclimate to OT-based threats in the long run.
- Second, document everything. You have to take notes on observations, decisions, and results every time you exercise. This paper will assist you in determining areas of deficiency and enhancing subsequent simulations.
- Third, emphasize realism. You are to structure your scenarios on the real threat intelligence and previous events. This approach would make sure that your exercises are based on real-life OT-specific threats and not hypothetical ones.
- Fourth, encourage collaboration. It is necessary to establish a setting where the participants feel free to give insights and feedback. This transparency enhances the process of learning and increases the coordination of the team.
- Last but not least, perform post-exercise reviews. This should be done by analyzing performance, determining areas of weakness, and making improvements. This is an ongoing feedback loop that would help you to manage OT-specific threats in a better way.
Benefits of Controlled OT Security Exercises
Secured and monitored activities bring great benefits to companies. They do not just increase the level of security, but also operational resilience. To begin with, they enhance incident response. Teams can learn how to identify, analyze, and act upon threats that are specific to OT بسرعة and effectively. Such preparedness decreases the time of response in actual cases.
Second, they improve communication. Different teams are united through exercises and promoted to collaborate. Consequently, the organizations are in a better position to react to a complex situation. Third, they determine vulnerabilities. Managed simulations indicate the flaws in systems, processes, and human beings. Thus, organizations will be able to deal with such gaps before they become exploited by the attackers.
Fourth, they endorse compliance. Most of the regulations compel organizations to show readiness to counter cyber risks. Workouts are an indication of defensive security. Lastly, they develop self-confidence. The teams will receive practical experience and acquire the skills to resist OT-specific threats in practice..
Conclusion
Safe and controlled exercises are also very important in ensuring that the OT environments are secured. They enable the organizations to make tests to their defenses, enhance their coordination, and train for actual incidents. This means that by concentrating on OT-specific threats, you will be able to make your simulations relevant and effective.
In addition, such exercises assist you in balancing between security and the continuity of operations. They give a systematic way of risk identification without interfering with the vital processes. Thus, exercises should be designed regularly and conducted in every organization that uses OT systems.
Frequently Asked Questions
1. What are OT-specific threats?
OT-specific threats are those aimed at industrial systems such as SCADA, PLCs, and control networks. These attacks use the weaknesses specific to the environment of the operation technologies.
2. Why do controlled exercises matter in OT security?
controlled exercises cause the simulation attacks to enable organizations to simulate attacks safely. They assist the teams in training on actual incidents without interfering with the operation or the safety.
3. How often should organizations conduct OT security exercises?
Organizations should conduct exercises regularly, preferably quarterly or biannually. Regular drills make sure one is ready to counter the changing threats and enhance the general security stance.