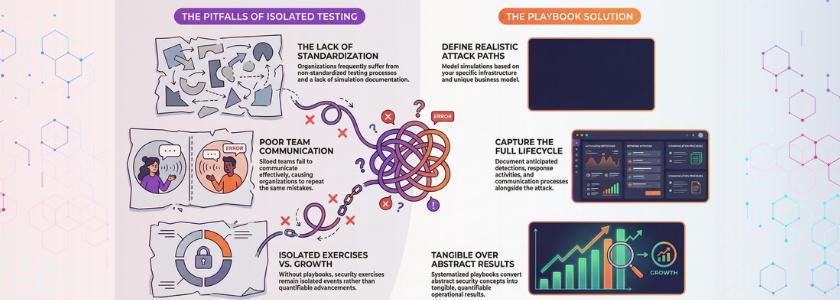
Red team or blue team exercises are often conducted in isolation by security teams, but seldom translate into sustained operational benefits. Consequently, detection gaps recur, and response delays recur on a quarter-by-quarter basis. This is the place where Purple Team Playbooks generate clarity, order, and long-term betterment within your company.
You also create controlled and repeatable attack scenarios, which actually test your defenses, as opposed to performing a one-off simulation. So you no longer have to guess when you are ready, but prove it through evidence. By looking at security this way, you transform Purple Team Playbooks into a living system that continually hones people, procedures, and technology.
Purple Team Playbooks: Establishing Structured Security Testing Paths
Purple Team Playbooks allow you to define realistic attack paths based on your infrastructure and business model. But you do not merely simulate compromise as you also capture anticipated detections, response activities, and communication processes. This causes all engagements to give tangible results rather than abstract ones.
In addition, repeatability motivates maturity in your security departments. You repeat the same scenario several times, compare performance metrics, and determine improvement trends. Subsequently, you have ceased reactive firefighting and have developed a structured capability that has solidified your overall security position.
Integrating Purple Team Playbooks Into Daily Security Operations
You would want to incorporate Purple Team Playbooks in daily SOC operations rather than focus on them as project-based activities. As analysts practice what they have been tested on, they react to actual alerts in a less hesitant way. Simulations, as a result,t have a direct boosting effect on day-to-day detection and incident handling.
Furthermore, you are expected to match findings of playbooks with SIEM tuning, threat hunting hypotheses, and response drills. Thus, the improvements do not stop at reporting but progress in the form of operational changes that mitigate risk continuously. Such integration means that your purple team activities will have enduring defensive effects as opposed to a transitory appearance.
Aligning Playbooks With Business Risk
In creating Purple Team Playbooks, you have to base every scenario on a business-critical asset or operating risk. As an illustration, you can fake identities of credential theft of the financial systems or data exfiltration of the customer databases. Hence, the leadership has the full picture of why the exercise is important and why it safeguards the revenue and reputation.
Besides, you would need to convert technical findings into business impact. Rather than providing only a report on the gaps in logs, you provide how failure to detect delays on time may result in regulatory fines or downtime. Consequently, executives view security testing as a business strategy, as opposed to a technical trial.
The MITRE ATT&CK framework has documented thousands of real attacker behaviors that help teams build repeatable detection tests in their Purple Team Playbooks.
Designing Realistic and Controlled Scenarios
Successful Purple Team Playbooks reflect the way attackers behave in the real world as they stay within rigid operational constraints. You pretend to be privileged, or on the side, or someone who has phished their way in; however, you state your scope well to avoid interruption. You thus work out resilience without endangering the stability of production.
Also, you record anticipated telemetry before the commencement of execution. When the alerts do not beep in the simulation, then you are quick to realise where you are blind in the detection. In this way, the training emphasizes the success of the attacker instead of defensive validation and enhancement.
Defining Meaningful Performance Metrics
Good Purple Team Playbooks are based on factual indicators and not personal impressions. The measures that you are tracking on an individual per scenario basis are detection time, triage accuracy, containment speed, and communication efficiency. You will, as a consequence, have a clear indication of operational capability.
In addition, you compare measures in repeated executions of the same situation. When detection time drops significantly, you confirm measurable improvement; however, when containment slows down, you focus directly on optimizing the response process. Therefore, you develop your program based on real data instead of relying on assumptions.
Real Life Example:
This GitHub repository hosts a community-maintained Active Directory Purple Team Playbook that security professionals use as a repeatable reference for adversary emulation and detection testing.
Strengthening Collaboration Across Teams
Properly designed Purple Team Playbooks allow teams to work together rather than competing with each other. Instead of showing superiority, both parties concentrate on uncovering weaknesses and mutually fixing them. As a result, we enhance trust and spread defensive knowledge throughout the organization.
Meanwhile, you promote cross-functional visibility. SOC analysts observe attack simulations and discuss the findings with threat hunters, cloud engineers,s and incident responders. Consequently, teams create collective understanding regarding opponent conduct and defense anticipations.
Operationalizing Lessons Learned
You make Purple Team Playbooks the very best by transforming findings into actionable improvements as soon as completing each engagement. You do not put in reports in stores; you create additional detection rules, modify escalation paths, and modify response runbooks. Thus, all exercises enhance day-to-day activities.
Moreover, you do debriefing sessions in a structured manner when the insights are still fresh. The team members talk about the confusion areas, interruptions in communication, and the gaps in tooling. As a result, you convert weaknesses into prioritized and owned initiatives of improvement.
Evolving and Scaling the Program
Established organizations view Purple Team Playbooks as living documents and not as fixed assets. Since the methods of attackers are evolving, you should read and refresh your situation regularly. Consequently, your testing framework remains in line with the emerging threats and new technologies.
In addition, you roll out the program step-by-step departmentally and environmentally. You could start with a simulation based on endpoint and then proceed to cloud, identity, and supply chain. As a result, your security maturity is built in an organized and long-lasting fashion.
Conclusion
Finally, repeatable security verification is between mature and reactive organizations. In spite of the fact that numerous teams participate in individual drills, it is only training that is well-organized and quantifiable that develops a durable defensive prowess. By developing scenarios based on risk, improving measurements, and continuous process optimization, you create an evidence-based and continuous improvement security culture.
Frequently Asked Questions
1. Why should organizations prioritize repeatable purple team scenarios?
Repeatable scenarios should be considered important in organizations as consistency results in a quantifiable change. When the teams test a similar attack path many times, they can realize performance trends and confirm defensive improvements.
2. How often should a company run purple team engagements?
The engagement schedule that you should have should be according to the exposure to risks and the capability in operation, but quarterly testing is good with most organizations. Frequent repetition makes detection logic, response coordination, and communication workflows always sharp.
3. What makes a purple team program successful in the long term?
Bluesky success requires the support of the executive, quantifiable metrics, and disciplined follow-through on the findings. Although simulations indicate flaws, long-term improvement can only be achieved when the teams take corrective measures at the same time.