Hackers are quick; hence, you need to be quicker. This case study demonstrates how a company in the GCC improved its security practices and reduced the time to detect by 70% with the help of Purple Teaming Threat Detection.
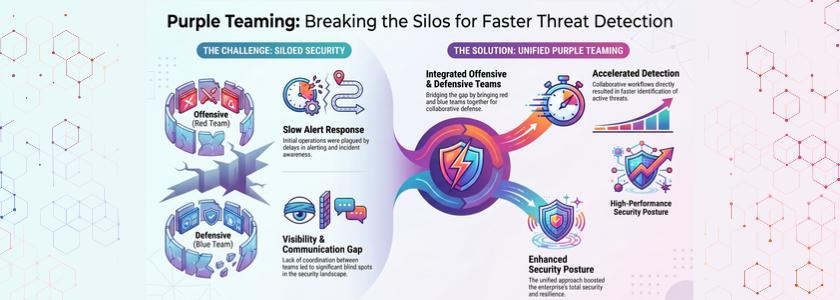
The enterprise was initially plagued by slow alerts, a lack of communication, and visibility. But as soon as they embraced Purple Teaming Threat Detection, they brought their offensive and defensive teams together. This allowed them to not only accelerate detection but also boost their overall security.
Let’s see how they did it – and what you can learn from it.
Why Traditional Detection Failed—and What Changed with Purple Teaming Threat Detection
Initially, the enterprise heavily used team-based approaches. Red team attacked, and blue team defended. But the teams were isolated, leading to red tape. As a result, it took hours or days to detect threats.
And threat detection tools raised alerts, but it wasn’t clear which ones to focus on. As a result, they had problems with alert fatigue and overlooked threats.
Enter Purple Teaming Threat Detection. Both the Red and Blue teams worked together. This allowed them to detect and fix issues in real time and improve detection processes.
Real Life Example:
The Colonial Pipeline ransomware attack forced the shutdown of fuel supply due to delayed threat detection. Attackers remained undetected long enough to deploy ransomware across systems. Faster detection (via purple teaming) could have reduced the impact significantly.
Key Steps That Reduced Detection Time
1. In-the-Moment Teamwork
First, the company removed any barriers to communication. They moved away from siloed operations and into a collaborative environment for red and blue teams.
- The red team continuously attacked as if it were real
- Blue team monitored and responded instantly
- Red and blue teams provided feedback
This resulted in a better response. In addition, the analysts learned what attackers do, improving their analytic abilities.
2. Regular Testing
Earlier, the company did security testing only once in a while. But this wasn’t sufficient to keep up with the latest threats. As a result, they are now testing every day via Purple Teaming Threat Detection.
- Imitated phishing, ransomware, and lateral movement
- Validated detection rules in real-life scenarios
- Validated security controls regularly
As a result, they found vulnerabilities more quickly. Also, they patched their detection holes.
3. Better Detection Rules and Use Cases
At first, their rules in the SIEM generated too many false positives. But with Purple Teaming Threat Detection, they improved their detection rules.
- Removed redundant alerts
- Adjusted rules to attack simulations
- Focused on high-risk behaviors
So, analysts didn’t have to waste time sifting through false positives. So they identified and stopped real threats quicker.
4. Improved Incident Response Process
But it’s not enough to detect threats. You must act quickly. So the company has improved its incident response processes.
- Automated alert triaging
- Established escalating procedures
- Reduced manual intervention
As a result, the response time was greatly reduced. And incident analysts responded to incidents more quickly and confidently.
Tools and Techniques That Made the Difference
The company employed simulation platforms to simulate threats. These were used to simulate the effectiveness of their detection mechanisms.
2. Threat Intelligence Integration
They incorporated threat intelligence sources. This allowed them to better detect known attack patterns.
3. Centralized Monitoring Systems
They consolidated logs and alerting in a single view. So, analysts could better see what’s happening in the environment.
4. Automation and SOAR Integration
They automated repetitive tasks. As a result, security analysts were free to focus on critical threats. These changes all contributed to improving Purple Teaming Threat Detection and measuring success.
Measurable Outcomes and Business Impact
Since adopting Purple Teaming Threat Detection, the company has delivered great outcomes:
- 70% shorter detection time
- Increased alert accuracy
- Decreased false positives
- Enhanced team collaboration
- Improved security stance
In addition, the firm was assured of its capability to deal with sophisticated threats. Thus, the organisation provided funding for more purple teaming.
According to the Ponemon Institute, organizations with mature security practices reduce breach lifecycle significantly. Strong collaboration between teams plays a key role in faster detection and containment. Purple teaming directly supports this by aligning offensive and defensive strategies.
Challenges Faced and How They Were Solved
1. Resistance to Change
Originally, teams didn’t want to collaborate. But leadership fostered a sense of “we-ness”. Thus, the team adopted the approach.
2. Skill Gaps
Analysts were not familiar with offensive techniques. So, the organisation trained and practised.
3. Tool Integration Issues
Having multiple, integrated tools was complex. But they were also streamlined and made processes consistent.
4. Measuring Success
Initially, they had difficulty in measuring success. Then, they established KPIs such as detection and response.
By overcoming these obstacles, they got the most out of Purple Teaming Threat Detection.
Real Life Example:
The Equifax data breach exposed 147 million records due to missed alerts. A security tool detected activity, but the team failed to act on it in time. Purple teaming could have validated alerts and improved response coordination.
Lessons You Can Apply to Your Organization
If you’re hoping to achieve similar success, take a proactive approach. First, enhance team communication. Together, you can detect threats more quickly. Second, continually test your security. Cybercriminals are constantly changing, so you need to respond accordingly.
Third, less is more in alerts. Too many alerts are distracting. And lastly, automate and train. Good analysts and tools are a great help. By doing this, you can achieve the same success Purple Teaming Threat Detection has achieved.
Conclusion
As this case study demonstrates, the old methods of security simply aren’t enough. But Purple Teaming Threat Detection is an effective approach. Through collaboration, process, and technology, you will be able to increase your detection speed.
In this case, transitioning to Purple Teaming Threat Detection in this GCC enterprise led to quicker detection, improved communication, and enhanced security. So, if you’re to have a chance of keeping up with hackers, you need to do the same.
In short, time is of the essence. The quicker you identify threats, the more secure your business will be.
Frequently Asked Questions
1. What is Purple Teaming in cybersecurity?
Purple teaming is a blend of red team (offensive) and blue team (defensive) activities. It encourages co-operation to enhance detection and response times.
2. How does Purple Teaming improve detection time?
It promotes team-to-team feedback. This means that organizations quickly detect and continuously improve their detection capabilities.
3. Is Purple Teaming suitable for all organizations?
Yes, it can be applied by any size organisation. But they need to tailor the process to their needs and capabilities.