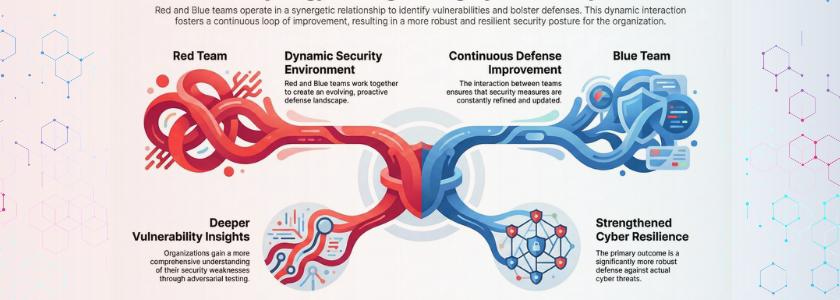
Red and Blue Teams create a dynamic security environment that continuously improves defenses. Organizations leveraging Red and Blue Team gain deeper insights into vulnerabilities and strengthen overall cyber resilience.
A red team behaves as a real attacker and proactively attempts to intrude into systems via real-world techniques. Hence, they imitate phishing, exploit vulnerabilities, and navigate within networks to test security loopholes. In addition, they are concerned with detecting vulnerabilities that conventional security tools can hardly detect.
Conversely, a blue team is concerned with the protection of systems and the detection of suspicious information on the fly. Their functions include checking logs, examining alerts, and responding promptly to accidents. Consequently, they enhance the limits of defense and minimize the possibility of effective cyberattacks within the organization.
How Red and Blue Teams Improve Security Collaboration
Red teams are offensive in their thinking, whereas blue teams are defensive, and this contrast creates an effective learning cycle. Their combined effort in forming a joint security approach is stronger when both teams work together. Organizations use Red and Blue Team collaboration to bridge security gaps more promptly and efficiently.
In this model, red teams do not work in isolation but provide attack insights to blue teams. Blue teams then enhance detection and response policies based on actual attack behaviors. Through this cooperation, organizations achieve sustained improvement and increased cyber resilience over time.
How red teams operate in real environments
Red teams do not just attack with automated scans and simple testing to plan the attack. They begin by collecting information about the intended environment and determining the possible points of weakness. After that, they mimic actual attack paths and test the depth to which they can attack the systems without detection.
In addition, they do not issue warnings since they wish to determine the reality of the effectiveness of defenses. Consequently, organizations become realistic in the behavior of attackers and the vulnerability of a system. This process aids in enabling the security teams to plan better against advanced and persistent threats.
Real Life Example:
The Colonial Pipeline ransomware attack showed that attackers used compromised VPN credentials to access systems and deploy ransomware, exactly like red team entry techniques
How blue teams defend and respond effectively
Blue teams constantly scan systems to identify potentially threatening and unusual behavior. They examine logs, comb through warning signs, and react promptly to the incidents in order to cause minimal harm. Thus, they are highly significant in the overall security of the organization.
They also enhance security measures according to the experience of the events and simulations of attacks. Therefore, they increase visibility and minimize blind spots in the environment. By doing this in advance, there will be more effective defenses and a faster reaction to the emerging threats.
Real Life Example:
In a real incident in Oldsmar, Florida, defenders quickly detected and reversed unauthorized access to a water treatment system, showing how blue teams respond to threats in real time
Why organizations need the Red and Blue Team approach
Organizations face high-level cyber threats that can easily circumvent conventional security systems and defenses. Thus, they require both offensive and defensive surveillance to remain safe. This is why Red and Blue Teams are critical in contemporary cybersecurity approaches.
By combining these two strategies, organizations can identify weak areas and address them before attackers can exploit them. Additionally, they establish feedback mechanisms that strengthen their overall security posture. As a result, organizations stay better equipped to handle advanced and dynamic cyber threats.
According to Verizon Data Breach Investigations Report, 74% of breaches involve the human element, highlighting the need for continuous attack and defense testing.
Common challenges and how to overcome them
It is an issue that many organizations face since the red and blue teams tend to operate in an isolated manner without effective communication and coordination. Nevertheless, such a deficiency in cooperation lowers the quality of testing and defense measures. Thus, teams should be ready to exchange knowledge and collaborate to increase results.
Moreover, a shortage of money and unprofessionalism can slacken the security work. This means that organizations ought to invest in training, tools, and processes. Such investment assists in enhancing coordination and also guarantees better outcomes of security undertakings.
Benefits of combining red and blue teams
When the organizations work together with both of the teams, they will have a realistic and holistic look at their security posture. Red teams point out the weaknesses, and blue teams strive to fix them and prevent them. Thus, this alliance forms a more robust and resilient cybersecurity system.
In addition, the constant collaboration increases the speed of detection, response, and efficiency. Consequently, the organizations lower risks and increase their capacity to deal with cyber threats. This will make security more offensive and less defensive as time goes by.
Role of continuous testing in Red and Blue Teams
Constant testing is critical for ensuring effective cybersecurity defense in contemporary organizations. Companies do not conduct a single set of tests but continuously assess systems for new weaknesses and vulnerabilities. Red and Blue Teams help guarantee ongoing improvement and increased preparedness.
In addition, regular testing enables organizations to keep up with evolving attack methods and changing threat environments. As a result, they stay ahead of attackers and reduce the risk of breaches. This sustained effort strengthens the overall resilience and sustainability of security.
Conclusion
There are two different roles of red and blue teams, but they have one objective, which is to strengthen the security posture of an organization. The red team detects the vulnerabilities by acting like an attacker, whereas the blue team defends the systems by detecting and reacting to the threats. Thus, such a balance forms an all-inclusive and working security strategy.
Nevertheless, organizations perform optimally when they go beyond segregation and adopt cooperation. They achieve continuous learning, accelerated improvements, and better defenses by a Red and Purple Team approach. Consequently, they remain vigilant and able to stand and stand against current cyber threats with a sense of security.
Frequently Asked Questions
What is the main role of a red team?
Red teaming is performed to mimic actual cyberattacks to determine the weaknesses and the effectiveness of the defenses of an organization to overcome real-life attacks.
What does a blue team do in cybersecurity?
A blue team is concerned with the monitoring systems, the detection of threats, and the response to the events in order to safeguard the organization against cyberattacks.
Why are Red and Purple Teams important for organizations? Red and Purple Team also assists?
organizations in enhancing security by integrating offensive testing and defensive measures to keep it improved and enhance protection against emerging threats.