Cybersecurity is often likened to a war, and this is where the roles of Red and Blue teams come into play. With evolving cybersecurity threats, there is a need for organisations to have a structured method of protecting their assets. Many people hear these terms often but can’t always grasp the distinction between the two or why they are both important.
At a high level, the Red and Blue team approach consists of two teams: the “attackers” and the “defenders”. But there’s more to it than that. Knowing the difference can help you build better security policies, enhance detection skills, and ultimately, better respond to threats.
Understanding the Core Roles in Red and Blue Teams
First, let’s look at the roles of the two teams. While their goal is to enhance security, their approaches are very different.
What Does a Red Team Do?
A red team is like an attacker. That is, it emulates cyber attacks to assess the security of a system. So, rather than just theoretically testing the security of a system, a red team will try to hack a system, pinpoint vulnerabilities, and bypass security measures. A red team will, for instance:
- Send emails to test employees’ security vigilance
- Exploit software vulnerabilities
- Attempt to steal sensitive data
This allows an organisation to feel vulnerable as if they were a hacker. Importantly, it can help to identify vulnerabilities before they are exploited.
What Does a Blue Team Do?
In contrast, a blue team is the defensive team. They monitor for threats, detect malicious activity, and respond to incidents. The blue team is on its heels, looking to prevent attacks by the red team. A typical blue team will:
- Monitor network traffic and logs
- Review alerts and anomalies
- Respond to incidents and breach containment
So, the blue team keeps security controls in place and effective.
The Main Difference Between Red and Blue Teams
So, the question is, what is the main difference between a Red ana d Blue team? The difference between the Red and Blue teams is the end goal and methodology.
- The red team attacks to discover weaknesses.
- The blue team protects and repels attacks.
But it’s not just that. The red team is the offensive (hackers), and the blue team is the defensive (protectors). As a result, the two teams work together, rather than in competition.
And the red team operates periodically with red team exercises, whereas the blue team operates continuously. This timing is also important in the way companies organise their cybersecurity.
Why Organisations Need Both Teams
It might seem possible to simply go with one team. But only having one team is problematic. With only a blue team, you may be able to protect against known attacks, but you may overlook potential vulnerabilities. But with only a red team, you will identify vulnerabilities, but won’t defend against them.
So, a meld of the two is needed for security. The Red and Blue team strategy means organisations can not only discover threats, but also defend against them.
Real Life Example:
A Kroll red team exercise on an international organisation exposed weak passwords, poor monitoring, and phishing vulnerabilities that could disrupt major business operations.
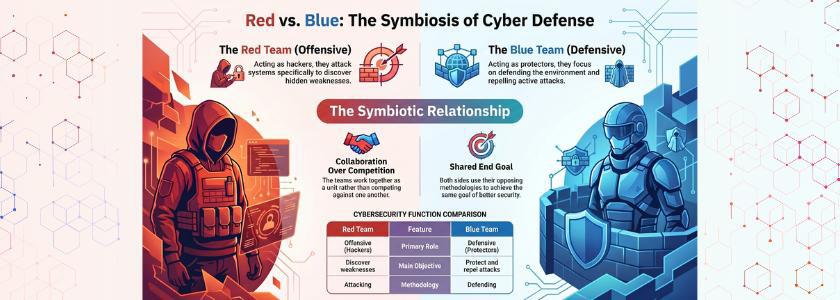
How Red and Blue Teams Work Together
While they have distinct purposes, the teams shouldn’t operate in a bubble. The optimal approach is for them to work together. For example, following a red team exercise, the results should be shared with the blue team. This way, the blue team can enhance its defences based on the actual attack.
Also, companies often use a “purple team” approach, where the teams collaborate during simulations. This results in more rapid improvement in attack detection and response. This approach turns cybersecurity from a reactive to a proactive and ongoing improvement process.
Real Life Example:
The United States Department of Defence uses red team assessments and exercises like cyber war games to evaluate and improve defensive readiness.
Skills Required for Each Team
Looking at the skill sets can also help to differentiate between the two teams.
Red Team Skills
Red team practitioners must have offensive skills. They need to be creative and behave like hackers. For this reason, they often have expertise in:
- Ethical hacking
- Penetration testing
- Social engineering
- Exploit development
- Blue Team Skills
Blue Team Skills
Blue team analysts, on the other hand, have a defensive and analytical mindset. They must be able to solve problems and be detail-oriented. They generally concentrate on threat detection and monitoring.
- Incident response
- Security information and event management (SIEM)
- Digital forensics
- For this reason, enterprises typically create separate teams that are highly trained.
Benefits of the Red and Blue Team Approach
This approach has several benefits for organisations.
First, they increase threat recognition. Through the red team’s continuous attacks, the blue team improves in detecting attacks. Second, they reduce risk. By discovering weaknesses, companies can patch them before they’re exploited.
Third, they improve Incident Response. The blue team learns how to respond to cyber attacks and experiences what it’s like to defend against them. And finally, they foster a security culture. Staff recognises threats and management invests in security.
According to IBM, organisations that extensively test security systems (including simulated attacks) identify breaches faster and significantly reduce overall incident costs.
Common Challenges and How to Overcome Them
However, this approach isn’t without challenges. Ineffective communication is a common problem. Without communication among teams, there will be missed learning opportunities. So, frequent reporting and sharing are important.
Resource constraints are another issue. Not all companies have resources for teams. But organisations can begin by outsourcing red teaming or training their employees.
Furthermore, there are companies that view red team exercises as an attack, rather than an opportunity for improvement. This can stifle efforts. Rather, the leadership should see these exercises as opportunities to learn.
Conclusion
The distinction between a Red or Blue team is more than an attack versus a defence team. It’s a comprehensive cybersecurity approach that includes penetration testing and protection.
The red team seeks vulnerabilities, and the blue team ensures vulnerabilities do not become vulnerabilities. Together, they form a dynamic system that adapts to the ever-changing threat environment.
If you want to improve your cybersecurity, you must employ multiple strategies. You must have both views. That’s how today’s enterprises remain safe in an ever-evolving digital environment.
Frequently Asked Questions
1. What is the primary goal of a Red and Blue team?
A Red and Blue team’s main objective is to enhance cybersecurity through offensive and defensive measures. The red team tests the system to discover vulnerabilities, and the blue team defends to detect and counterattack.
2. Can small organisations use the Red and Blue team approach?
This approach can be used by small organisations. They can contract red team services or train their blue team. Even if they do it poorly, they will be better off.
3. What is a purple team in cybersecurity?
A purple team is a blend of the red and blue teams. The teams work together to enhance detection and response, and to drive security improvements.