An attack of ransomware is not a one-step process. Rather, attackers use a systematic route that begins with initial access and concludes with either encryption of data or data exfiltration. So, to effectively defend your organization, you need to know and emulate the whole ransomware kill chain. This will enable you to identify the weak points before they are exploited by attackers.
Most organizations, however, continue to test isolated scenarios, rather than complete attack paths. Consequently, they overlook important loopholes in detection and response. Attackers, therefore, take advantage of these blind spots and are successful. As a measure to prevent this, you need to model realistic attack flows and exercise your abilities in all stages.
Why Simulating the Ransomware Kill Chain Matters
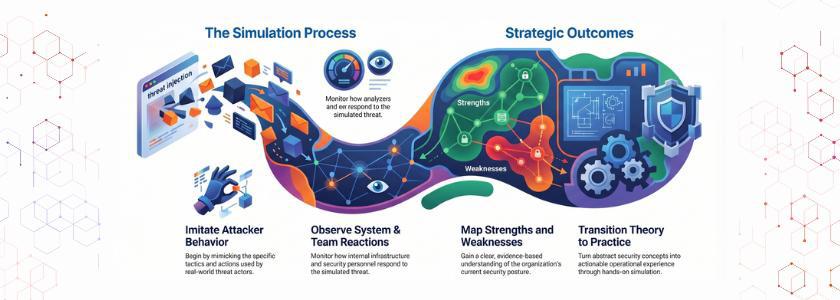
The full ransomware kill chain is a simulation that enables you to transition between theory and practice. To begin with, you imitate the way attackers behave. Next, you can see the reactions of your systems and teams. Consequently, you get a clear understanding of your strengths and weaknesses.
In addition, this is a method that enhances inter-team coordination. As security tools issue alerts, you need to respond promptly and precisely by your team. You can make sure that your team is not only able to detect the threats but also react to them using real-life scenarios of an attack. As a result, your organization will be strengthened.
According to Sophos, 66%of organizations were hit by ransomware in 2023, showing how widespread these attacks have become.
Stage 1: Initial Access Simulation
Phishing emails, stolen credentials, ls, or exposed services are typically the starting point for attackers. So you need to be realistic in simulating these entry points. E.g., you can test phishing attacks or try to use credentials.
At this phase, you will assess the effectiveness of your controls against unauthorized access. Also, you see whether your team is able to spot suspicious activity at the initial stage. In case the attack is not detected by your system, you will be well aware of how to make your system better.
Stage 2: Execution and Persistence
Attackers get access and run malicious code to create persistence. Hence, you have to emulate the performance of malware in your setting. Meanwhile, you would check the detection and blocking of execution by your endpoint protection tools.
Moreover, this step also evaluates your monitoring skills. In case your tools are not producing alerts, then you need to make adjustments. This way, you enhance visibility within your network.
Real Life Example:
The NotPetya ransomware campaign infected multiple sectors globally and used tools like PsExec and credential theft to move across networks
Stage 3: Privilege Escalation and Lateral Movement
Once a foothold has been secured, attackers will seek greater privileges. Then, they cross systems to ensure that they reach out. Thus, your simulation should have privilege escalation and lateral movement techniques.
At this stage, you put your controls to the test in deterring unauthorized access to critical systems. As an example, you can simulate credential dumping or attempts to access remotely. In case your defenses are unsuccessful, the attackers will be free to roam.
But, as you go through the entire ransomware kill chain, you spot these vulnerabilities. As a result, you will be able to have more robust access controls and segmentation. In addition, you can make sure that the attackers will not be able to move freely in your environment.
Real Life Example:
Maersk was crippled by the NotPetya attack (2017), where ransomware spread laterally and disrupted global operations completely
Stage 4: Data Discovery and Exfiltration
The current ransomware attacks usually entail the stealing of data prior to encryption. Thus, you need to emulate data discovery processes and data exfiltration. The step will aid in your learning of how attackers find sensitive information.
Moreover, the need to classify data is emphasized in this step. Once you are aware of the location of sensitive data, you can safeguard it. As a result, your organization is able to reduce the possible damage.
Stage 5: Encryption and Impact Simulation
The last phase is to encrypt information and disrupt operations. So you will have to imitate this influence. Although you are not supposed to cause damage, you can test the reaction of your systems to the attempts at encryption.
This stage tests your incident response plan. As an illustration, you make sure that your team puts in place actions ensuring the rapid isolation of affected systems. And you also evaluate your speed of recovery.
Testing Detection and Response Capabilities
Running attacks is not the only aspect of simulating the ransomware kill chain. Rather, it aims at testing your detection and response abilities at all levels. Hence, you need to gauge the speed of recognition of threats and action by your team.
The first is the analysis of detection times. Next, you measure the effectiveness of responses. Delays: In case of delays, you find the cause of the delay and rectify it. This means that you minimise response time and damage.
Continuous Improvement Through Iteration
You can not count on one simulation. Rather, you need to redo it on a regular basis. Every upgrade enables you to improve your defenses and adapt in accordance with the emerging threats.
Moreover, there is a continuous development of methods by attackers. Hence, your simulations will have to develop as well. It is through updating scenarios that you will make sure that your organization is prepared.
Common Mistakes to Avoid
Most organizations do simulations, but they are unable to get meaningful results. First, they are concerned not about processes, but only about tools. Nevertheless, it is not possible to prevent ransomware with the tools.
Secondly, they do not pay attention to collaboration. Detection and response will not be effective without teamwork. As such, you will need to engage all the stakeholders involved.
Third, they do not analyse post-exercise. You cannot improve without going through results. This means that you will have to examine the results and make changes. These errors can be avoided to make the most of your simulations.
Conclusion
Ransomware is one of the greatest dangers to organizations in the present times. But it is quite possible to protect yourself against it by modeling attack scenarios in the real-world. You can test through the whole ransomware kill chain and identify the concealed vulnerabilities and enhance your ability to respond.
Thus, simulations should not be an option. Rather, you need to incorporate them in your security plan. In this way, you can create resistance and be ahead of attackers.
Frequently Asked Questions
1. What is a ransomware kill chain?
A ransomware kill chain refers to a series of actions that are undertaken by attackers, starting with initial access to data and ending with data encryption or exfiltration.
2. How often should organizations simulate ransomware attacks?
Simulations need to be regularly performed in an organization, preferably every quarter or whenever there has been a significant change in the system, to ensure that the organization is ready to face the changing threats.
3. What is the main benefit of simulating the full kill chain?
Recreating the entire kill chain will assist in detecting security deficiencies, enhancing the detection and response, and increasing the overall resilience to ransomware attacks.