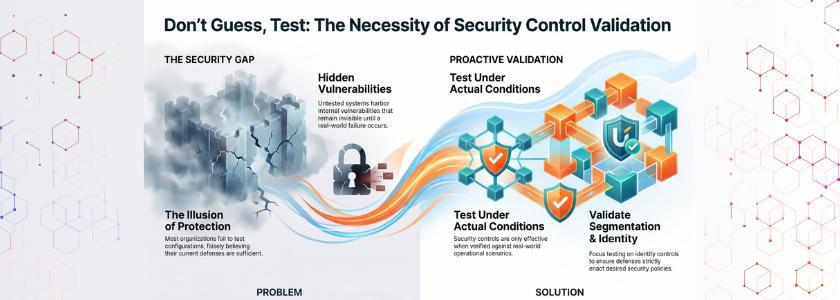
Contemporary companies are heavily investing in security controls, but still, the loopholes seem to exist where attackers can bypass the security measures. You can use segmentation, identity verification, and set stringent access control, but unless they are properly validated,d you cannot be sure they are working. This means that to test your environment, you have to be proactive. That is why you have to validate segmentation and identity controls in an organized and continuous manner.
In addition, hackers do not comply with your conjectures. Rather, they take advantage of vulnerable configurations, inconsistent policies, and unnoticed access routes. Therefore, companies that never validate their controls tend to discover their problems only at the end of the day. Conversely, by being proactive in testing your defenses, you are able to detect and resolve issues before they get out of control.
Why You Must Validate Segmentation and Identity Controls
The security controls can only be effective when you test them under actual conditions. Nonetheless, most organizations do not test their configurations and believe that they have the right ones. Consequently, the system has vulnerabilities that lie within it. Thus, you need to check and validate segmentation and identity controls to make sure that your defenses enact the desired policies.
The purpose of network segmentation is to restrict the lateral movement of identity controls to restrict unauthorized access. Nevertheless, misconfigurations can weaken them. An example of a rule that is too permissive, which can enable attackers to move between systems. Likewise, lax identity checks may also provide access to unauthorized users.
According to Verizon’s Data Breach Investigations Report, 74% of breaches involve the human element, highlighting the need for strong identity validation.
Understanding Segmentation in Practice
Segmentation breaks up your network into areas that are under control, lowering the attack surface. Nonetheless, merely segmentation does not imply security. You need to check whether or not those pieces indeed isolate essential assets.
The first thing is to check your segmentation rules. Make sure that they are in line with business requirements and security policies. Simulate possible attack paths then. This will enable you to observe whether an intruder can move sideways across segments or not.
Best of all, you need to validate segmentation and identity controls with each other. The identity controls cannot prevent attacks in case of failure of segmentation. This means that the two layers need to be evaluated together in order to attain effective protection.
Real Life Example:
Capital One improved network segmentation after its 2019 breach by tightening access controls and isolating sensitive workloads to prevent lateral movement.
Strengthening Identity Controls
The basis of security today is identity controls. They dictate access to resources and the circumstances. But the gaps in identity systems are usually left unattended and are exploited by attackers.
To begin with, implement stringent authentication. Multi-factor authentication can greatly minimize the chances of unauthorized access. But you have to find out if it is reliable over all systems.
Then, user privileges. Several organizations provide too much permission, which is risky. Hence, use the principle of least privilege and ensure users can only access the necessary information.
In doing so, you are proactively validating segmentation and identity controls, and it will ensure that identity systems are in line with your overall security approach.
Real Life Example:
Google’s BeyondCorp model validated identity-based access by eliminating VPN reliance and enforcing strict user
Evaluating Access Policies Effectively
The policies of access determine the interaction of users with systems. Nonetheless, security loopholes are usually caused by unplanned policies. So you need to consider them.
Begin by reviewing policy consistency. Make sure that regulations are subject to equal application. Lack of consistency in policies may result in unintentional access.
Then, experiment with real-world conditions. As an example, make attempts to use restricted resources with various roles and devices. This assists you in verifying that policies have restrictions that are enforced appropriately.
A combination of these steps effectively checks validate segmentation and identity controls, and makes sure that access policies are working as desired.
Common Challenges and How to Solve Them
Validation is a challenge that is commonly experienced by organizations. To begin with, they do not cope with visibility. They lack a clear understanding of systems, thus being unable to detect the weak points. Thus, the monitoring tools that offer complete visibility should be implemented by you.
Secondly, teams tend to be siloed. This restricts the level of collaboration and delays improvement. But you can address this by co-locating teams to work towards a common objective and promote communication.
Third, validation activities might not be consistent. Other organizations conduct tests just once, and this makes it less effective. Instead, you ought to put in place continuous validation procedures.
By solving these issues, you can regularly validate segmentation and identity controls and stay in a favorable security posture.
Best Practices for Continuous Validation
You must have an organized strategy to be successful in the long term. Initial: Have clear aims for each validation activity. This will make sure that what you do is focused and effective.
Secondly, realistic attack simulations. These simulations indicate the performance of your controls in the face of pressure. Above all, do it on a regular basis. Incessant testing makes certain you constantly validate segmentation and identity controls with the changes in threats.
Future of Security Validation
Cybersecurity is an ever-changing phenomenon, and companies need to keep up with it. Defenses in place are not sufficient any longer. In its place, ongoing validation will be critical.
New technologies will include AI and automation, which will improve the validation processes. Nevertheless, human skills will be highly important. You need to read results, decide, and enhance strategies using insights.
Thus, organizations placing more emphasis on validation will have a huge benefit. They will detect the weaknesses at the initial stage and act properly. In doing so, you can be sure that you are continually validating segmentation and identity controls in an evolving threat environment.
Conclusion
Security controls can only bring value when they are effective. Thus, it is necessary to test and verify them. Segmentation, identity controls, and access policies are the foundation of your defense policy, but they need constant review.
When you validate segmentation and identity controls, you leave assumptions on assumptions. You find vulnerabilities and eliminate them beforehand, and tighten up your general security stance.
FAQs
1. Why is it important to validate segmentation and identity controls?
Validation is a way of making sure that your security controls are effective. Misconfigurations and gaps may go undetected without testing and put the risk of attacks at risk.
2. How often should organizations perform validation?
Validation should be done on a continuous or regular basis by the organizations. The frequent testing enhances a high level of security and responds to the changing threats.
3. What tools can help in validation?
Validation is assisted with the help of different tools such as network monitoring systems, identity management platforms, and simulation tools. Nevertheless, you need to use tools in combination with human analysis to achieve the most.





