Cybersecurity terminology can be quite confusing at times, and the red team is one such term. You may also question yourself as to why professionals use this particular color and what it symbolizes. More to the point, you might wonder how this term can relate to the actual security practice. This blog explores the origin of the red team while keeping everything simple and easy to understand, without making things complex or hard to comprehend.
First of all, the red team originated as a result of military tactics whereby armies distinguished themselves by color. Nevertheless, the meaning has changed a lot in cybersecurity. Now, we can anatomically decompose it and learn not only the name, but also the actual purpose and usefulness of this name to organizations today.
Origin of the Red Team and Its Historical Background
The red team can be traced back to war games in the military, which clearly explains the origin of the red team. Planners in these simulations separated forces into two groups, with one side taking the role of attackers and the other one the role of defenders. They usually referred to the offensive side as red and the defensive side as blue. This color system assisted teams in recognizing roles and strategies in exercises within a short time, further shaping the origin of the red team in modern practices.
In addition, this is a technique that militaries employ to practice their defense preparedness without actual threats. They developed simulated scenarios of attack and allowed the red team to reason like enemies. Consequently, they managed to discover weaknesses in advance of real conflict, which strongly reflects the origin of the red team and its relevance in cybersecurity today.
Subsequently, this concept was embraced by cybersecurity experts. Organizations borrowed the same idea since they required proactive defense strategies. Thus, the genesis of the red team became closely related to the field of ethical hacking and security testing.
How Red Teams Work in Cybersecurity
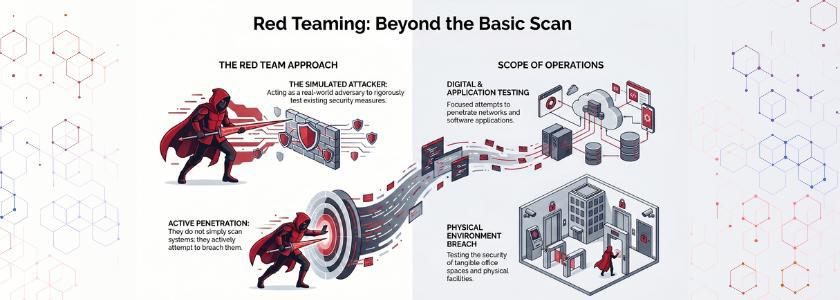
It is not sufficient to know about the name. You must also know what the red teams do.
The red team is a simulated attacker. They do not simply scan the systems, but instead, they make attempts to penetrate networks, applications, and even physical environments. They may, e.g.:
- Launch phishing attacks
- Exploit software vulnerabilities
- Attempt unauthorized access
- Test employee awareness
Consequently, organizations can have a realistic perspective of their security posture. Red teams are creative and flexible in their technique, unlike automated tools.
Moreover, the origin of the red team is also significant in this case, as it focuses on the adversarial way of thinking. Red teams do not merely test systems; they put assumptions to the test and uncover latent risks.
Real Life Example:
A financial institution’s red team simulated phishing emails and successfully captured employee credentials, proving human error as a major entry point.
Red Team vs Blue Team: Understanding the Difference
To have a complete picture of red teams, you have to juxtapose them with blue teams.
- Red Team: Plays as attackers and identifies weaknesses.
- Blue Team: Protects systems and reacts to the threat.
Red teams will imitate attacks, and blue teams will observe systems, read logs, and prevent attacks. The combination of them brings a balanced security approach.
Nevertheless, the genesis of the red team brings out an aspect. It demonstrates that organizations can not afford to rely on defense alone. Rather, they need to be vigilant and simulate attacks as an attacker would view their systems.
Thus, organizations applying a combination of teams enhance their safety much more quickly.
Why Organizations Need Red Teams Today
The number of cyber threats is increasing by the day. Hackers are sophisticated, and conventional defenses are normally lagging. Due to this, proactive strategies are required within organizations.
This is where red teams come in.
To begin with, they detect the vulnerabilities before attackers can take advantage of them. Second, they do not use theoretical risks, but they test real-life situations. Third, they assist organizations in becoming better at responding to incidents.
Also, the source of the red team reinforces the origin of the red team, reminding us that it is always better to be prepared than to simply react. Waiting to be attacked means you have already suffered damage. However, by simulating real-world onslaughts, organizations stay one step ahead of potential threats.
Real Life Example:
A red team exploited a Jenkins vulnerability and escalated access to full domain control in a real enterprise environment
Benefits of Red Teaming
Red teaming has several obvious benefits:
1. Realistic Testing
Red teams are as close to real attacks as can be. Thus, the outcomes are based on actual risks, rather than assumptions.
2. Improved Security Awareness
Attackers operate in a way that employees learn how to do it. Consequently, they get wary and vigilant.
3. Stronger Defense Systems
Organizations obtain vulnerabilities more quickly. They make the chances of successful attacks less likely as a result.
4. Better Incident Response
Teams get to know how to respond in stressful situations. This increases the efficiency and response time.
Most importantly, the source of the red team makes sure that testing is always geared towards real-world threats as opposed to hypothetical situations.
Common Misconceptions About Red Teams
Red teams are misconstrued by many people. Shall we dispel some of the myths?
- Myth 1: Red teams do not do anything other than hack systems. They, in fact, test individuals, procedures, and technology as a unit.
- Myth 2: Red teaming is the same as penetration testing. Even though the two are similar in that they both entail security testing, red teaming is more extensive and tactical.
- Myth 3: Red teams are only required by large companies.
Indeed, even small and medium-sized businesses are prone to cyber threats and will be able to use red teaming.
Once again, the source of the red team indicates that it does not merely aim at hacking, but at overall security enhancement.
The Evolution of Red Teams
Over time, the red teams have developed tremendously.
In the beginning, they primarily targeted technical attacks. But there are now modern red teams that comprise:
- Social engineering experts
- Physical security testers
- Cloud security specialists
This change is an indicator of shifting threat landscapes. Attackers do not use only one method, and red teams need to change.
Additionally, the source of the red team still steers this evolution. It makes sure that teams are able to think like opponents and are creative in their thinking.
Red team exercises replicate real-world attacker tactics across people, processes, and technology to uncover hidden security gaps.
How to Implement Red Teaming in Your Organization
In case you desire to employ red teaming, you ought to take a systematic process, keeping in mind the origin of the red team. To begin with, set specific goals. Choose what you wish to test: the network, applications, or employees. Second, select seasoned personnel who are aware of attacker behavior. Then, enable simulation controls without interfering with business processes.
Test results and analyze. Get bugs remedied and processes fixed. Lastly, do the same on a regular basis. This way, you use the actual intention of the creation of the red team, reflecting the origin of the red team, which is to constantly improve by realistic testing.
Conclusion
A red team can be an innocent term, but one that has a strong connotation, highlighting the origin of the red team. Its origin in military strategy influenced the way organizations deal with cybersecurity today. Through such a concept, companies are able to reason the way attackers do and enhance their protection.
Finally, the lesson of the red team is that you should have tested your defenses before they are tested by someone else, which emphasizes the origin of the red team. With this mentality, you are not just being reactive but proactive in your security—that is the difference.
Frequently Asked Questions
1. What is the main purpose of a red team?
A red team determines the vulnerabilities to security by recreating real-life attacks. It aids organizations in identifying vulnerabilities prior to actual attackers taking advantage of them.
2. How is red teaming different from penetration testing?
In penetration testing, the target is a particular system, whereas red teaming is more generalized. It challenges individuals, procedures, and technology in a real-world situation.
3. Why is understanding the origin of the red team important?
Receiving the background of the red team will make you see its purpose. It demonstrates that red teaming is not only technical testing, but it is also a strategic method in enhancing overall security.