The main aim of red teaming is to ensure the vulnerabilities are detected before they can be used by malicious actors. Organizations tend to believe that they have the security in place, but attackers are continuously developing new methods. The objective of red teaming assists in filling this gap by adopting the thinking of a possible opponent. Basically, it is a matter of thinking like the attacker whilst protecting your assets.
Moreover, another important goal of red teaming is to enhance the coordination of security, IT, and operational teams. When a red team carries out an attack simulation, the blue team (defenders) needs to react in real time. This exercise is not only a test of technology, but also an eye-opener for communication and incident response measures. The aim of red teaming is, therefore,e basically to ensure that an organization becomes strong enough to face any unanticipated threats.
How the Objective of Red Teaming Drives Security
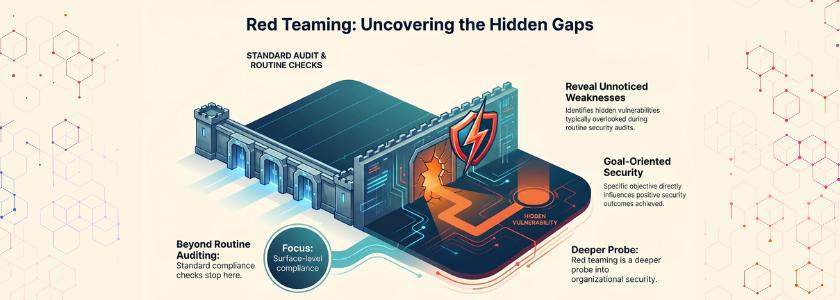
It is important to know the objective of red teaming as it directly influences the positive outcomes an organization can obtain. To begin with, red teaming helps to reveal unnoticed weaknesses that are usually overlooked during routine audits.
Second, red teaming is aimed at enhancing the response time in real security incidents. During an attack, time is of the essence, and organizations that train in real-life situations will react quicker and more efficiently. Thus, the objective of red teaming not only identifies issues but also makes the team more prepared and resilient.
Third, the other important advantage associated with the objective of red teaming is regulatory compliance. Cybersecurity has stringent requirements in industries like banking, healthcare, and energy. Red team exercises serve to assist organizations in illustrating that they proactively test and harden their security posture.
Real Life Example:
A UK national organisation’s red team exercise successfully gained employee credentials through targeted social engineering and network intrusion, revealing gaps in employee awareness and incident response readiness.
How Organizations Implement Red Teaming
The goal of red teaming is to accomplish it in a systematic way. Organizations usually adhere to a multi-step procedure that encompasses planning, execution, analysis and remediation.
- Planning: This stage involves the red team defining the scope of the exercise, identifying critical assets and gaining familiarity with organizational processes. This measure will guarantee that the exercise is realistic and may pose real-life conditions that can truly test defenses, fulfilling the objective of red teaming.
- Action: The red team plays an attack with various tactics, techniques, and procedures. These may involve phishing, network intrusions, physical intrusions, or insider threats. In this level, the blue team responds in real time to test their detection and response skills, which aligns with the objective of red teaming to evaluate readiness under realistic conditions.
- Analysis: After completing the exercise, all of the findings are documented by the red team and weak areas are noted with recommendations that can be taken. This analysis is based on technical weaknesses and gaps in operation, which support the holistic concept of red teaming.
- Remediation: Lastly, organizations respond to the suggestions of the red team. They close the holes in the software, update policies, train employees and enhance incident response plans. It is through this cycle that organizations can attain the goal of red teaming by converting insights into practical improvements.
Real Life Example:
During a red team engagement with a large gas‑industry group, testers used tailgating and impersonation tactics to bypass on‑site controls and access secure areas, uncovering physical security lapses.
Common Misconceptions About Red Teaming
However, as advantageous as it is, red teaming is occasionally misconstrued by organizations. Among the misconceptions is the fact that it is merely a technical exercise. As a matter of fact, the objective of red teaming involves human factors, processes, and communication channels. The other myth is that red teaming is only applicable in large corporations. Nonetheless, any company that deals with sensitive information or that requires vital processes can learn to anticipate vulnerabilities.
Some also think that red teaming is disruptive in nature. Whereas it imitates attacks, professional red teams follow strict rules to prevent operational damage. Indeed, the objective of red teaming ensures safety and continuity by identifying weaknesses in a controlled environment.
In a 2019 industry survey, 68% of IT security professionals said red team exercises were more effective than blue team testing at uncovering security weaknesses.
The Future of Red Teaming
The cybersecurity environment is changing quickly and so is red teaming. New attack surfaces are presented by emerging technologies like artificial intelligence, machine learning and cloud computing. Organizations must continue to perfect their strategies in order to accomplish their red teaming objective.
Moreover, the regulatory pressures and demands of stakeholders are increasing. Customers and investors are putting pressure on companies to show that they are taking proactive security measures. Red teaming fulfills these expectations by showing that organizations expect threats to occur and not as a response. Therefore, the red team’s aim is mainly to build trust and carry on with the business process.
Conclusion
Red teaming has a purpose and any organization that wants to ensure good security and operational resilience needs to understand the purpose of red teaming. Organizations discover untold vulnerabilities by simulating real-world attacks, enhancing response exercises, and cultivating a spirit of never-ending enhancement. From technical flaws to human mistakes, red teaming considers every aspect, making sure that defense is not just well-built but also flexible to new threats.
Finally, red teaming is not just about attack prevention, but it enables companies to foresee, react, and succeed in a multidimensional threat environment. Through such a proactive strategy, companies ensure that they protect their assets, reputation and attain long-term success in terms of security.
Frequently Asked Questions
1. What is the main goal of red teaming?
The primary aim is to replicate real-life attacks in order to find out the weak points of systems, processes and human behaviors. This objective will make sure that organizations are able to prevent real breaches, as well as respond to them appropriately.
2. How often should organizations conduct red team exercises?
Organizations are advised to perform red team exercises at least once a year or when there are major changes in infrastructure, processes or threat landscape.
3. Is red teaming only for IT security?
No. Red teaming deals with technical systems, physical security and human behavior. Red teaming has the objective of testing the entire organizational resilience, and therefore, it is useful to all the departments that handle sensitive assets or critical operations.