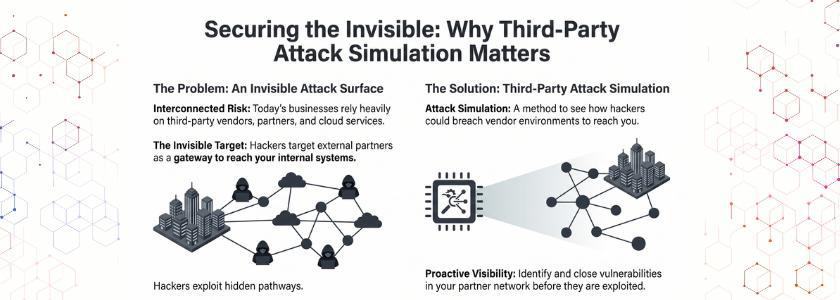
Today’s businesses rely on third-party vendors, cloud services, and partners. But this also presents an invisible attack surface that hackers target. That’s why third-party attack simulation is so important today. It enables you to see how a hacker could breach your vendor environment and get to your systems.
You don’t assume things; you simulate scenarios. This leads to discovering vulnerabilities not found in standard audits. And you boost your security readiness by identifying potential vulnerabilities. Thus, third-party attack simulation is no longer a best practice; it’s a necessity.
Why Third-Party Attack Simulation Matters in Modern Security
Third-party attack simulation is important because companies are no longer stand-alone. They have intricate networks of service providers. But each link can pose a risk.
Conventional security strategies are ineffective as they only consider internal elements. And hackers exploit weaknesses in external connections. So, there’s a need for an active approach to assess attack scenarios.
Also, vendors may have varying security levels. Thus, gaps arise that are exploited. For instance, one vendor may have strong authentication, but another may not. So, hackers take the path of least resistance. Finally, an attack simulation by a third party assists security teams in answering questions such as:
- Can attackers get in via a vendor account?
- What if a partner is breached?
- Where can they go in other systems?
Also, this approach fosters awareness within the organisation. So, security becomes proactive.
Real Life Example:
The MOVEit Transfer breach (2023) exposed sensitive data from hundreds of organizations by exploiting a third-party file transfer tool.
How Third-Party Attack Simulation Works in Real Environments
Third-party attack simulation simulates cyberattacks on customers’ systems and those of their vendors and partners. Rather than theorise, you experiment. Thus, you can understand your risks.
1. Mapping Vendor Ecosystems
You start by listing external vendors and partners. Then, you visualise the data flows. Additionally, you record access and integrations. This helps to establish visibility before testing.
2. Simulating Attack Entry Points
Then, you model how hackers can gain access via third-party apps. This could be via stolen passwords or vulnerable APIs. Thus, you test these thoroughly.
3. Testing Lateral Movement
Following an entry simulation, you test lateral movement. Moreover, you see if segmentation is effective. Thus, you know the true blast radius.
4. Assessing Detection and Response
And you measure the speed with which your security team picks up the attack. And you assess the response and its effectiveness. Thus, you discover monitoring and incident response gaps.
The NotPetya attack (2017) spread globally through compromised Ukrainian accounting software, showing how a single vendor can trigger widespread damage.
Key Risks Identified Through Third-Party Attack Simulation
Third-party attack simulation helps to reveal risks. They are not otherwise detected.
- Overprivileged Vendor Access: Vendors are granted excess access. But attackers abuse this to gain access to more of the system.
- Weak API Security: APIs connect multiple systems. As a result, poorly secured APIs are prime targets.
- Credential Misuse: Compromised vendor credentials can be used to circumvent security. As a result, identity security is key.
- Unmonitored Integrations: Integrations might not be monitored. Therefore, malicious attacks are not monitored.
- Fourth-Party Exposure: Your vendors may use other vendors. So risk is not under your control.
Business Benefits of Third-Party Attack Simulation
First, they gain a better understanding of their ecosystem. Secondly, they detect vulnerabilities before they are exploited. Also, they increase compliance with security requirements.
Secondly, security teams improve coordination. So, red and blue teams collaborate more seamlessly. This means strategies to combat and prevent security issues are quicker and more effective.
Third, businesses avoid financial and reputational damage. As a result, they prevent breaches due to vendors’ vulnerabilities. Lastly, executives are confident in their security decisions. Thus, cybersecurity expenditures are more efficient.
Practical Steps to Implement Vendor Compromise Simulation
To effectively conduct a vendor compromise simulation, you need a plan. Here’s a basic approach:
1. Identify Critical Vendors: Compile a list of all vendors who have access to sensitive data. Also, those with access to systems.
2. Classify Risk Levels: Next, determine which vendors pose a greater risk. For instance, payment card processing companies and cloud service providers are higher risk.
3. Define Attack Scenarios: Then, design attack scenarios. In particular, consider credential theft, API abuse, and phishing.
4. Execute Controlled Simulations: Having planned, run simulations in a safe environment. Thus, you won’t impact live operations.
5. Evaluate and Optimize: Lastly, assess results. And repair vulnerabilities and re-test systems frequently.
Why Traditional Testing Is Not Enough
Traditional security testing and monitoring are focused on internal systems. But cyberattacks don’t begin there. Rather, they start from external infrastructure.
So, third-party attack simulation is crucial as it mimics real-life attacks. Also, it identifies vulnerabilities that static analysis misses.
And finally, conventional approaches are one-off. However, attack simulation enables continuous improvement. This ensures security is dynamic and flexible.
Future of vendor compromise simulation
Ecosystem testing is critical to the future of cybersecurity. Thus, vendor compromise simulation will become a must.
And organisations will automate and use AI for simulation. As a result, threat detection and response will be quicker and more efficient.
Also, regulatory requirements will require more rigorous third-party risk assessments. So, companies that embrace simulation now will have a competitive edge.
Conclusion
Cyber attacks don’t recognise boundaries. Rather, they target vulnerabilities within vendor and partner networks. So, security within the four walls is not sufficient.
Third-party attack simulation can help you identify attack paths, dependencies, and fortify your security strategy. And it shifts security from passive to proactive protection. In short, this approach allows organizations to mitigate risks, increase visibility, and foster trust throughout their digital environment.
Frequently Asked Questions
1. What is a third-party attack simulation?
Third-party attack simulation is a cybersecurity exercise that simulates attacks on vendors and partners to test out vulnerabilities in external relationships.
2. Why is third-party attack simulation important?
It is crucial because hackers prefer to target vendors to breach organisations. So simulation identifies vulnerabilities before an attack.
3. How often should vendor compromise simulation be performed?
It should be done on a regular basis, particularly when new vendors are introduced or changes are made to systems to provide ongoing vendor compromise simulation.